Welkom bij
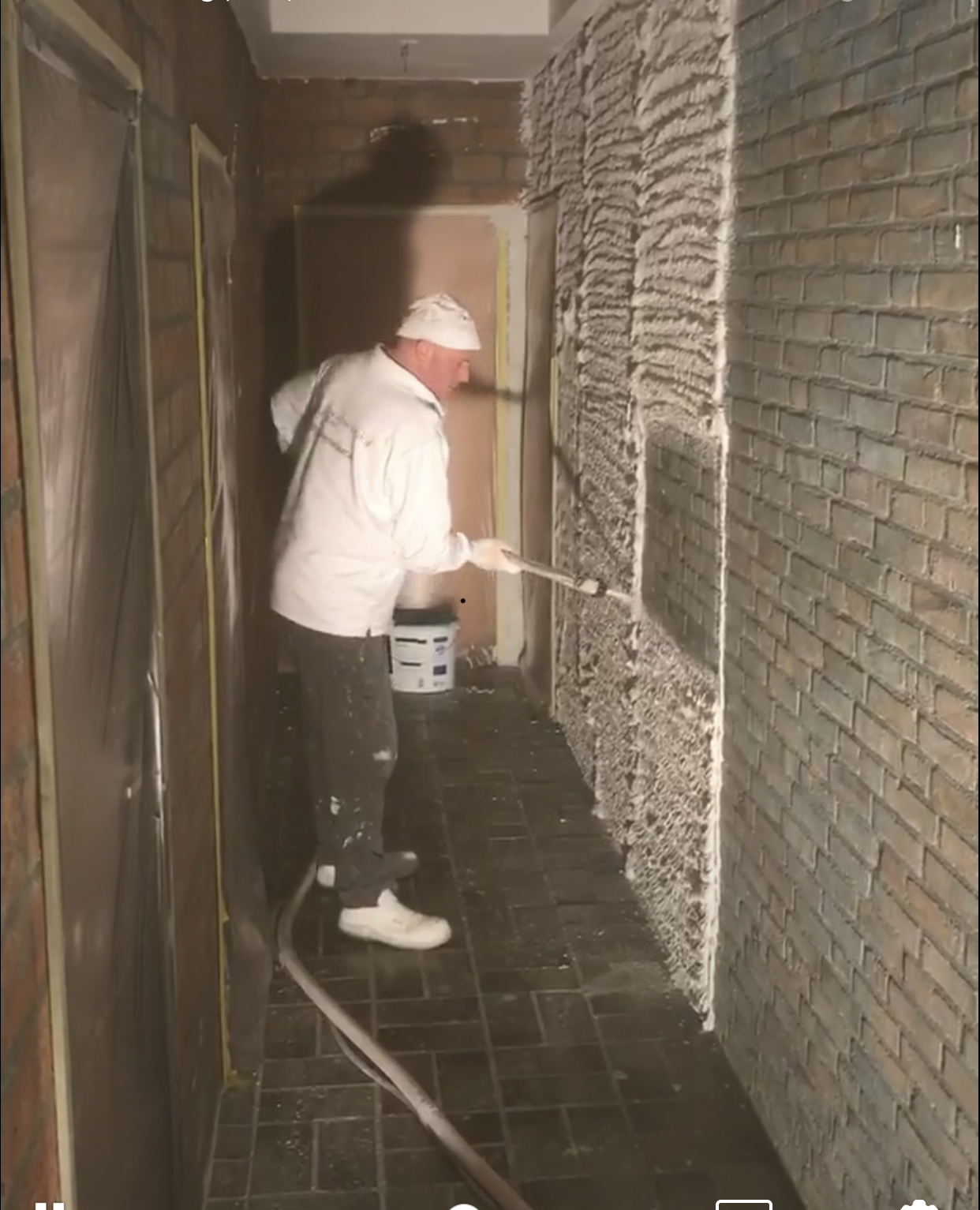
STUCADOORSBEDRIJF
VAN HARSSELAAR
"De afwisseling in mijn werk vind ik prachtig en de adviserende rol die ik heb als stucadoor geeft mij veel voldoening"
Nico van Harsselaar
Nico van Harsselaar
"De klant moet tevreden zijn! Dat is waar wij voor gaan"
Roel van Harsselaar
Roel van Harsselaar

Kwaliteit door ervaring
Stucadoorsbedrijf van Harsselaar is een klein bedrijf dat constante kwaliteit levert. Dit is de reclame van onze stucadoors. Door de jarenlange ervaring van Nico te combineren met de nieuwste technieken van Roel zijn wij in staat vakwerk te leveren. Daarnaast vinden wij het belangrijk om eerlijk en open te zijn. Afspraak = afspraak!
Nico & Roel
Onze diensten
Bekijk onze projecten